While technology has made our lives simpler, it has also brought criminality with it. Hackers have scammed tens of thousands of businesses and people during the previous years, and they are not planning to stop. Phishing emails have become the source of 91% of all cyberattacks. And the majority of data breaches take about six months to notice. The cybercriminals may have deleted all evidence of their involvement after those six months. According to a new Gallup poll, Americans are more worried about cybercrime than physical crime. These figures demonstrate how vulnerable data may become when it is kept on the internet.
Hackers are well-equipped with both technical knowledge and cutting-edge tech tools. This makes it simple to defraud billion-dollar corporations as well as ordinary people. Thus, it would be best if you start protecting yourself before anything bad happens.
How your information can be hacked

Your information can be leaked as easily as when you visit a blacklisted website. Although it may not appear to be wrong on the first move. However, keep in mind that these unintentional situations unlock the door to your information getting hacked, which can be detrimental to finances and business. Other times, it might be hackers sending harmful emails. These emails contain malware that gives a hacker access to your device to steal anything they want. More so, you should ensure that the identities of those with who you communicate via email have been confirmed, and Nuwber can help with that.
And have you ever noticed how some applications request access to your gallery, documents, or location? While some apps and websites make every effort to keep such information secure in their systems, hackers can find methods to infiltrate those systems. But your digital data will be protected, far from the reach of a hacker, if you follow the guidelines below and exercise extreme caution.
Always use multi-factor authentication.

When you open bank or medical accounts, this should be the first step. Set up two-factor authentication (2FA) on every account that holds sensitive information, whether it’s connected with finances or it’s simply social media.
For some, 2FA may appear to be a technically sophisticated step that only the savviest young tech brains can implement.
It isn’t.
This function is generally enabled with the click of a button inside your account. And it goes without saying that if you want to protect your assets, this is a no-brainer.
2FA is just a code that is texted to your phone or email each time you log in. You may also download an app like Google Authenticator, which will provide you with the code anytime you launch the app.
In a nutshell, it’s the second line of defense against hackers. Apart from having your usual password, they would also require physical access to your device to access the code.
According to one research, multi-factor authentication and encryption are the most difficult challenges for black hat hackers.
Learn to create good passwords.
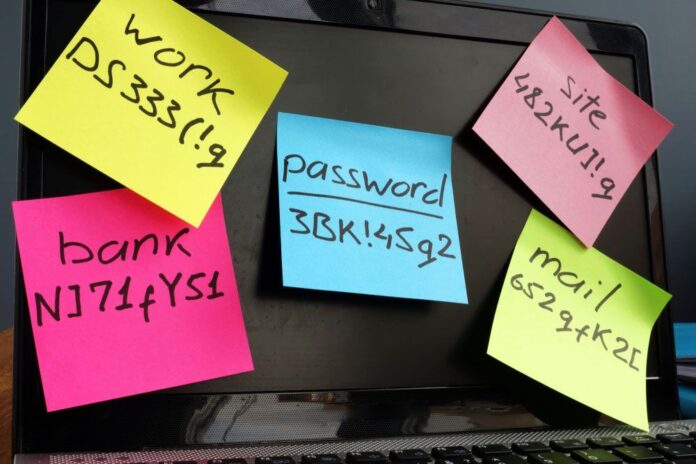
Your first line of protection is passwords, even though they can be hacked by experienced criminals. But you should know that It’s not the fault of the password itself; it’s we who fail to follow these fundamental rules when generating a new passcode:
- Create long, varied passwords: Passwords become significantly tougher the longer they get.
- Don’t use personal information: Hackers can locate personal information online, for example on social media accounts, and use it to hack into your accounts.
- Don’t use predictable patterns: Avoid predictable patterns, such as ABC or 123.
- Use different passwords: It may be easy to remember the same password. However, hackers will have access to numerous accounts if they breach one.
- Use a password manager: If remembering several lengthy, different passwords seems overwhelming, consider investing in a password manager such as LastPass or Keeper.
Understand how Phishing scams work.

Hackers’ most common tactics include phishing and social engineering. While some hackers are eager to exploit the first software flaw they discover, most believe that the human mind is the most susceptible computing system of all. It is much easier to persuade someone to provide over-sensitive information than to identify and exploit a software weakness.
Fortunately, phishers are constantly faced with obstacles if they want to dupe someone who has been schooled on their methods. Here are a few pointers for spotting a masked hacker:
- Beware of alarming emails: Hackers tend to capitalize on your emotions. Therefore, they frequently increase the urgency in their emails. They may inform you that your account has been hacked or that it will be terminated if you do not act quickly. Before you click anything, take a deep breath and look for irregularities. Take time to check whether it’s true from a different source.
- Check for suspicious email addresses. Hackers can replicate a company’s email style, but they typically can’t send it from a legitimate company email account. For example, a hacker may use the email ‘@theinstagram.team’ instead of ‘@instagram.com’ in an Instagram copyright infringement fraud. To remain on the safe side, you might want to verify every email sender you’re not familiar with.
- Check for terribly constructed grammar: Phishing efforts are frequently filled with strange jargon or poor grammar. If something doesn’t feel right, that’s because something’s not right. To make your grammar check a lot easier, download the Grammarly app.
Thieves can also design phony banking apps and distribute them through the App Store. Before installing an app, make sure to look at the number of reviews it has. It is most certainly not legitimate if it seems like an ‘official’ banking app and has few ratings and comments.
Buy encryption software.

Encryption software is now widely available and reasonably priced. This program encrypts your computer’s data and activities, making it far more challenging for hackers to get your details.
There are several forms of encryption software. Some encrypt particular files, while others encrypt your entire device, while others, such as a VPN, encrypt your internet activity.
Never use public wi-fi.
If you visit public venues such as libraries or coffee shops where a password is not required to use the internet, you put yourself in danger. Hackers might have easy access to your personal information if your wifi connection is not secured.
Even if your banking password isn’t kept on your computer, they can still obtain personal information about you that could help them get access to some of your accounts.
If connecting to public wi-fi is inevitable, be sure to use VPN.
Update and patch your devices.
Updating and Patching are required regularly for all of your devices, especially those connected to the internet. When it comes to dealing with security issues or software vulnerabilities, updates may be of great benefit. These system flaws are the entry points hackers look for when attempting to get unauthorized access to your information. Updating and patching all of your devices will secure your data while also bringing you up to date on the newest technologies.





